Bletchley Park, Allied Code-Breaking Center
Bletchley Park, the Enigma, and the Bombe
The German government used the Enigma machine to
encrypt and decrypt their military communications
during World War Two.
The Enigma was an electro-mechanical cipher machine based
on rotors.
It was a commercial system widely used by corporations and
governments starting in the early 1920s,
the German government used specially modified versions.
The UK and the US knew about the Enigma system, but had
concluded that it was impractical to break.
Then some Polish cryptanalysts arrived in the UK,
bearing the solution — they had reverse-engineered
the rotor wiring patterns using pencil and paper,
and they had designed a code-breaking machine.
They in turn were using some information gathered by
French intelligence.
Giving a workable solution, the British devised systems
to break the Enigma traffic.
This cryptanalysis and intelligence program,
known as Ultra,
was a huge aid to the Allied war effort.
The Allies carried out the work at
Bletchley Park,
a former country estate in England.
The official historian of British intelligence during
the war has estimated that while the Allies would have
defeated Germany anyway, Ultra shortened the war by
one to four years and saved millions of lives.
The Allies knew how the system worked as it was based on a commercial design. The Enigma used a set of rotors, each of which applied a unique encryption operation. The initial design had five rotors (the naval system had six). The encryption and decryption process was based on selecting three of them in some order. Later designs had more rotors, by the end of the war the naval system used four rotors out of a set of eight.
Enigma wasn't the only German machine cipher. The UK used "Fish" as a code word for a series of German teleprinter stream ciphers, done with the Lorenz SZ machines and similar. They had called the first one "Tunny" as in tuna.
Amazon
ASIN: 0116309334
The rotors were discs about 10 cm in diameter with 26 brass, spring-loaded contact pins in a circle on one face, and 26 brass contact plates on the opposite face. Each rotor performs a substitution cipher based on the wiring connecting the two sets of contacts. But the rotors were wired differently than in the commercial version.
A set of 26 letters in alphabetical order appear around the rim of the rotor. A gear-like plate on the pin face allows the user to rotate the rotor into one of 26 positions. A ratchet disc on the pin face allows the machine to advance the rotor one position at a time.
The first picture below shows a later 4-rotor naval Enigma. The four rotors appear near the top, they are currently rotated into position RDKP. The keyboard is toward the bottom, between it and the rotors is an array of lamps. When you press a key, an electrical signal is sent through the stack of rotors to light one of the lamps.
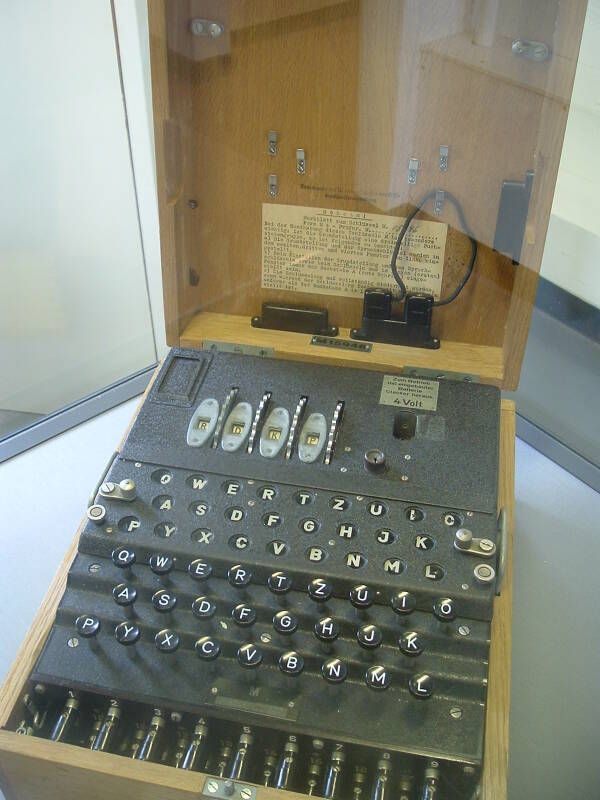

The second picture above shows a partially disassembled rotor. The spring-loaded contact pins are at far right. The green wires connect them to the circle of contact plates. The lettered rim and gear-like setting ring are at far left.
Each position of a single rotor applies a unique substitution cipher based on its internal wiring. The machine is loaded with the specified order of three or four rotors from the set of five to eight, each rotated to the specified starting position. Pressing one of the typewriter-like keys sends an electrical signal through the stack of rotors, through a reflector plate at the end (which adds its own substitution), and back through the stack of rotors to light one of the indicator lamps.
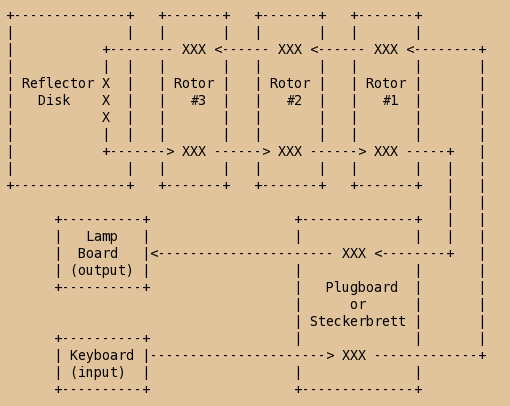
The setting for the Enigma machine, analogous to the key in a modern cipher algorithm, consists of the selection and order of rotors (what the Germans called the Walzenlage), the "roll-over" ring setting (or Ringstellung) for each rotor, and the cabling of the plugboard (or Steckerverbindungen) on its front panel that applied further permutations. Each "XXX" in the diagram below represents one substitution cipher operation.

General Heinz Guderian in the Battle of France with a communications team using an Enigma machine.
The configuration applies a unique monoalphabetic substitution cipher. Such a system could be broken with a few dozen characters. However, the rotor positions change with every letter, meaning that a different substitution cipher is applied at each letter through the message. The right-most rotor moves once with each letter. With each full rotation of a rotor, it moves the rotor to its left by one position. The "roll-over" or Ringstellung specifies just where this rotor moves the one to its left. Enigma applies a polyalphabetic substitution cipher with a period of about 17,000 letters before its rotors would return to their original positions and apply the same substitution as used for the first letter. However, messages were no more than a few hundred letters each.
The result is that the simplest Enigma, where you select three out of five rotors, has 158,962,555,217,826,360,000 possible initial settings.
The electromechanical Enigma machine is analogous to today's cipher algorithms, making the combined details of its setting analogous to an encryption key. The number of settings of a three-of-five rotor Enigma system is a little larger than the number of 67-bit keys:
267 = 147,573,952,589,676,412,928
268 = 295,147,905,179,352,825,856
However, the Enigma implemented a polyalphabetic substitution cipher while today's cipher algorithms combine substitution (or confusion) with permutation (or diffusion), meaning that you can't simply estimate difficulty of attack by comparing the keyspace.
The idea of attacking this system would seem to be pretty hopeless. However, French intelligence had collected information on the procedures used to encrypt messages, and they passed these along to Polish intelligence and their Biuro Szyfrów or Cipher Bureau. The Polish cryptanalysts Marian Rejewski, Jerzy Różycki and Henryk Zygalski were able to reverse-engineer the wiring of the rotors through theoretical mathematics, and they started breaking Enigma-encrypted messages in December 1932. They also designed the Kryptologiczna Bomba or Cryptologic Bomb, a device used to search for Enigma settings.
In late July 1939, just five weeks before Germany began World War Two by invading Poland, staff of the Biuro Szyfrów met with cryptanalysts of France and Britain and described how they had been breaking Enigma messages. They explained their procedures and the design of Rejewski's Kryptologiczna Bomba. The British cryptanalysts came from the Government Code and Cypher School.
The Government Code and Cypher School was based at Bletchley Park, 80 kilometers north of London.
Bletchley Park
This is the Mansion at Bletchley Park. The records on the place go back to the Domesday Book of 1086 The present mansion, an odd mix of architectural styles, was built after its purchase by Sir Herbert Samual Leon in 1883.

It passed from the family's hands to a builder who was planning to tear it down for a housing estate. Then Admiral Sir Hugh Sinclair, director of British Naval Intelligence 1919-1921 and founder of SIS, commonly known as MI6, purchased the mansion and surrounding 23 hectares of land with his own money.

The site was within a short walking distance of Bletchley railway station, with frequent connections to London. There were high-volume communication links via telephone and telegraph to London. The main road from London to the north and northwest passed nearby. Bletchley was also on the east-west railway connecting Cambridge and Oxford, universities expected to supply many of the code-breaking staff formally trained in mathematics. They joined a staff with diverse skills including linguistics, chess, and crossword puzzle solving.
The mansion was soon surrounded by hastily-built wooden structures referred to as "huts" and simply numbered. Later, several numbered "blocks" were built from brick. Above you see the end of the mansion and part of Hut 4. Hut 4 was occupied by Naval Intelligence, it was where they analyzed decrypts of German Naval messages.
Messages were intercepted at radio listening stations. These would be apparently random 5-letter groups transmitted by Morse code. The sheets of intercepted messages were all delivered by motorcycle dispatch riders initially. Later in the war, some listening stations were connected by teletype to Bletchley park.
When an intercepted message arrived, it was first processed for traffic analysis using the meta-information about the message such as time, frequency, length apparent transmitter location based on signal strength and direction finding, and possible recognition of the Morse operator's "fist". That's the distinctive Morse "accent", small variations in how that operator forms Morse characters.
It then went to cryptanalysis in which various techniques were applied to try to find the Enigma settings and decrypt the message.
If it could be decrypted, it went to the appropriate intelligence group for analysis of whatever meaning could be derived.
The finished product was then sent to MI6 or the Secret Intelligence Service and to intelligence chiefs in the relevant ministries. Later in the war, intelligence was sent directly to some high-level commanders in the field. The source would be obscured for that last category, with a cover story giving credit to some other source. Some deliberately visible scouting missions were sent to "discover" German positions already known from decrypted traffic.
The name "Ultra" came from this program being classified as "Ultra Secret", above Top Secret, and the Allies imposed strict limits on the use of the information to protect the source. If the Germans realized that the Allies could read Enigma traffic, they would change their procedures for using it and work on a replacement system.
Huts and Blocks
Hut 12, seen below, was used for Intelligence Exchange and Education.

Here, left to right, are Huts 3, 6, and 1.

Hut 3 (red) housed Intelligence. This is where they translated and analyzed decrypts of German Army and Air Force messages.
Hut 6, at center above and shown in the two pictures below, housed Cryptanalysis of German Army and Air Force ciphergrams.
Hut 1, at right above, was the first hut built. It went up in 1939 and initially housed a radio intercept station. This was called Station X, sometimes used later to refer to the entire Bletchley Park operation. The wireless station was moved to the nearby village of Whaddon so as to avoid drawing attention to its large wire antennas. Hut 1 was later used for administrative purposes. The first Bombe was initially installed in Hut 1.


This is Hut 6.
Below is Hut 3, where the Intelligence division translated and analyzed decrypts of German Army and Air Force messages.

Hut 6, the grey structure beyond the red Hut 3, housed Cryptanalysis of German Army and Air Force ciphergrams.

Below is Hut 8, where Naval Intelligence analyzed the decrypts of German naval messages.

Here we're looking into a window at the end of Hut 8.

Hut 6, at left below, housed cryptanalysis of German Army and Air Force cryptograms.

Alan Turing lived in "the Cottage", seen here. The Cottage sits beside the carriage house and the Mansion. The turret with the windows at top led to his room.

Dilly Knox, John Jeffreys, and others lived in other rooms of the Cottage.
While GCHQ, the Government Communications Headquarters, had mostly moved out in 1946, they continued to use this training facility into, I think, the early to mid 1980s. It looks like a medium-sized battered elementary school. This is up the rise beyond H block.

H Block, seen here, is in worse shape.

Below we are walking from H Block down between D Block (visible to the left) and E Block (off to the right).
D Block housed Traffic Analysis, Intelligence Exchange, and Naval Intelligence.

Here we see B Block at left leading into E Block.
B Block housed Air Intelligence and Naval Intelligence.
E Block handled communication in and out of Bletchley Park. It also housed BRUSA, the British-U.S. liaison program.

Exhibits
B Block now contains several exhibits, including the reconstructed German wireless station seen here.

The British Y Service intercept operators used these HF receivers to collect the intercepts attacked by the cryptanalysts.

In June 1941 the German military began using the Lorenz SZ or Schlüsselzusatz (cipher attachment) systems. These attached to a teletype machine and applied a Vernam stream cipher to its output data stream. The Lorenz SZ machine had twelve rotors, they generated a pseudorandom key stream which was exclusive-ORed with the 5-bit-per-character bit stream generated by the teletype machine. The output cipher stream modulated a frequency-shift keying radio transmitter.
Below is a Lorenz SZ42 machine at left, and the associated Lorenz T32 teleprinter at right. The Lorenz machines were built in small numbers, needed only at major command sites, and so only a few survive today.

The Lorenz SZ system was used beginning in the middle of 1942 for communication between German High Command in Berlin and the Army Commands across Europe.
On 30 August 1941, the Army Command in Athens sent a Lorenz-encrypted 4,000 character message to Vienna. It was not received correctly, and Vienna sent a cleartext message asking for a retransmission. The operator in Athens made a number of changes in the message, including replacing some words with abbreviations and therefore slightly shortening the message. Then the big error: the second message was transmitted with the same key settings.
The cleartext request from Vienna alerted Bletchley Park to pay special attention to the pair of messages. The error in Athens provided a depth that allowed Bletchley Park staff to discover the two plaintexts and the key.
From then through the following January cryptanalysts worked to reverse engineer the Lorenz SZ machine design. This has been described as one of the greatest intellectual feats of the entire war.
The British had code-named this system "Tunny", and they then built the Colossus computer to break Tunny. This was the world's first programmable electronic computer. It used thermionic valves (called vacuum tubes in American English) to perform calculations and Boolean operations. The first Colossus was operational by December 1943, ten of them were in operation by the end of the war.
The Bombe
The British cryptanalysts built a functional replica of the German Enigma machine, following the work done by the Poles before them. The goal was to discover the daily setting (or key) for a specific German military network. The device was called a Bombe, and two explanations are given for its name:
First, and probably most likely, this was the name given by the Polish mathematicians turned cryptanalysts as they discussed the problem over an ice cream dish known as a bomba.
A less convincing claim is that the name had to do with the ticking sound made by the machine as it worked through the possible keys, stopping and ringing a bell when it found a solution.
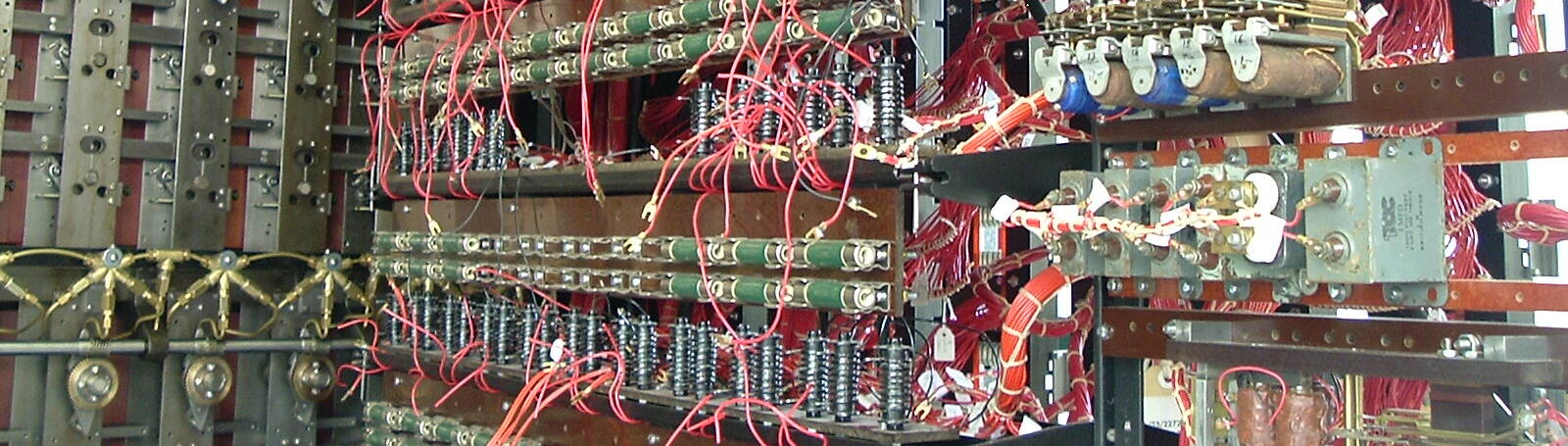
Here are pictures of the rear of a Bombe:
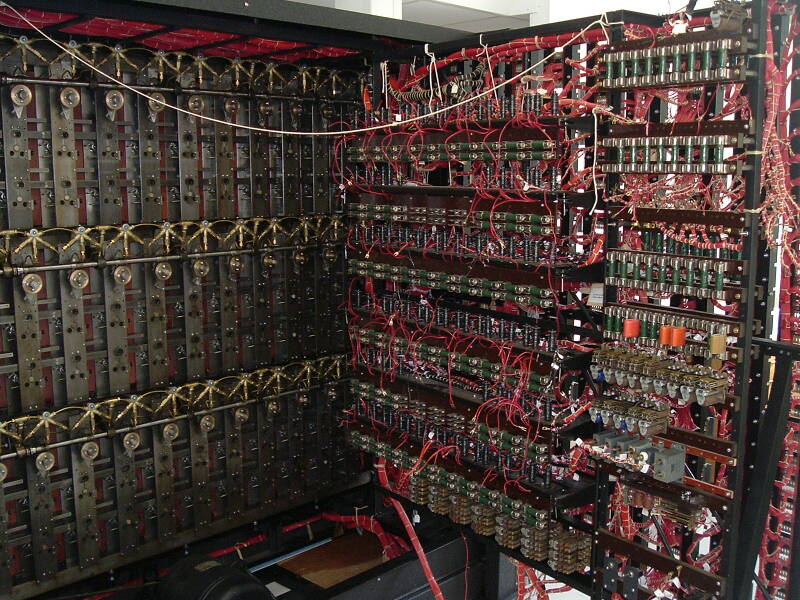
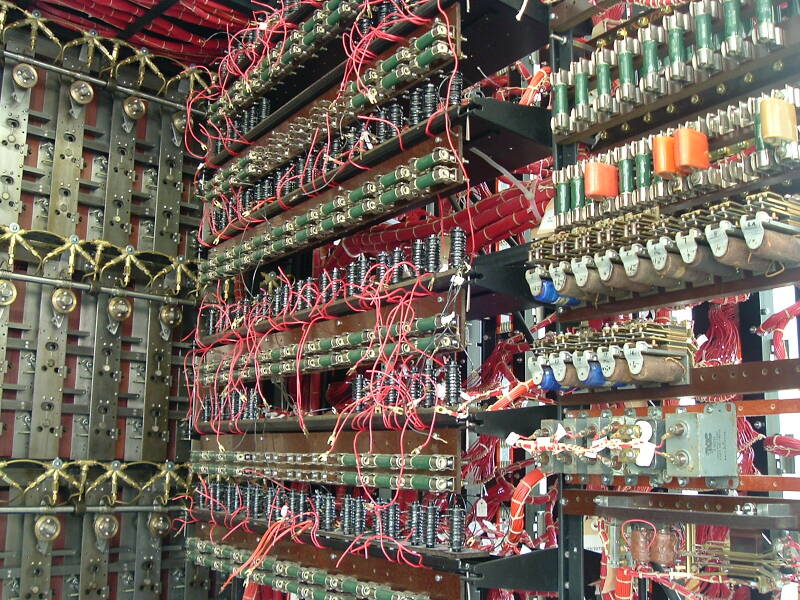
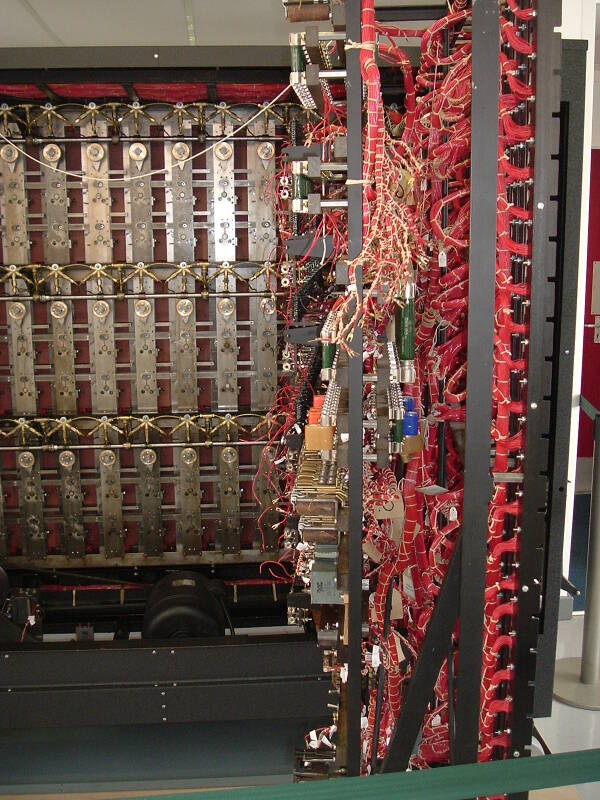
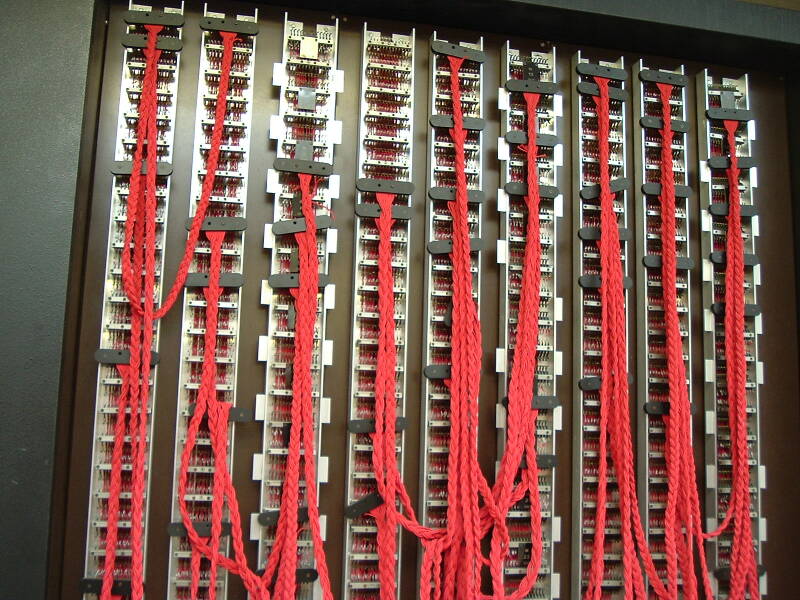
The front of each Bombe held 108 drums. Each drum simulates a rotor, so a column of three drums simulates one Enigma-equivalent device. Each Bombe then simulates 36 Enigma machines. Or, given the point of the Bombe, 36 possible initial settings for a three-rotor Enigma.


The U.S. also built Bombes, specializing in 4-rotor systems to attack the German naval Enigma. National Cash Register of Dayton, Ohio, was the main manufacturer for this project.
The Bletchley Park code breaking operation was moved to RAF Eastcote in 1946, where some Bombes were already based. Government Code and Cypher School was renamed Government Communications Headquarters or GCHQ in 1952. It remained at Eastcote until 1954, when GCHQ moved to Cheltenham.

Today you can visit Bletchley Park, it's open daily. The National Radio Center is located within Bletchley Park, and the National Museum of Computing is nearby.
How Were the Allies Able to Break Enigma, Lorenz, and other Axis Cipher Systems?
There were minor cryptographic weaknesses in the Axis cipher systems. However, key management is always the most difficult part of using cryptographic systems. Despite the German reputation for careful design and meticulously following procedures, even the German military failed to design a good key schedule and then they continuously made operational errors.
If the German military can't do key management, it must be awfully difficult.
Weakness in the Cipher Design
The cryptographic weakness in the Enigma design is that
an output character must differ from the
corresponding input character.
Put simply, if the ciphertext output is A,
then we know that the cleartext input could not
have been A.
The ciphertext looks highly random, but it does
leak some information — character by character, it tells
us what the cleartext could not be.
However, this is a very minor weakness, and if the Germans had used the system correctly, the Allies could not have discovered the keys and decrypted messages.
There were some systematic key design weaknesses, and even more significantly, systematic operational errors. The Nazis had a good cryptographic system, but they did not know how to use it correctly.
As far as strength against brute-force attack, the Enigma would have been adequately strong against the technology available to the Allies if used correctly. The U.S. SIGABA cipher system (also known as the M-134-C, ECM Mark II, CSP 888/889, and ASAM VI) had a much larger key space, 248.4 as commonly used, 295.6 as used on the POTUS-PRIME link between US President Franklin Delano Roosevelt and UK Prime Minister Winston Churchill. There was concern about SIGABA technology falling into Axis hands — not because it would provide any advantage for breaking the SIGABA cipher (see Kerckhoffs' principle) but because it might suggest improvements in the Enigma system.
- SIGABA: Cryptanalysis of the Full Keyspace, Mark Stamp and Wing On Chan, Cryptologia, v31:202-222, 2007
- Cryptanalysis of SIGABA, Wing On Chan, Master's thesis, San Jose State University, 2007
- Cryptanalysis of the SIGABA, M Lee, Master's thesis, University of California Santa Barbara, 2003
- "La cryptographie militaire", in Journal des sciences militaries, Auguste Kerckhoffs (1835-1903), vol IX, pp 5-38, Jan 1883, in which he proved that if the security of a cryptosystem relies on the secrecy of the algorithm, it is weak and could be improved.
Key Design Flaw #1
The first key design flaw was that the Germans specified that no rotor order should repeat within one month. So, that component of their key was not really random, and the number of possible keys decreased during a month. If an attacker can do enough brute-force work to break keys early in the month, or otherwise discover early keys (espionage, operator error), the required amount of work decreases as the month progresses.
Constraining the key in this way is as foolish as believing that a random system (throwing dice, flipping coins, observing fairly shuffled cards) somehow has a memory of past events! The probability of each random event is independent of previous events, and so today's key should not be constrained by those of the past one to thirty days.
Key Design Flaw #2
Even more significantly, and still on the rotor order, the Germans specified that no rotor could occupy the same position two days in a row. This also made things much easier for the attackers.
Consider the Army / Air Force system, where the rotor order was three rotors out of a set of five. Given free choice of all three rotors, as the Germans allowed themselves only on the first day of the month, you have 5 choices for the first rotor, 4 remaining choices for the second rotor, and 3 remaining choices for the third and final rotor. So, a total of 5×4×3 = 60 possible rotor orders.
However, if it is any day of the month after the first one,
in the German system, your choices are very limited.
Let's label yesterday's rotor sequence as
123 and the two unused rotors
as 4 and 5.
Today's allowed rotor choices are limited to the
following, where a red
rotor choice
violates this rule, and a
grey background
indicates an invalid rotor sequence:
123
|
124
|
125
|
132
|
134
|
135
|
142
|
143
|
145
|
152
|
153
|
154
|
213
|
214
|
215
|
231
|
234
|
235
|
241
|
243
|
245
|
251
|
253
|
254
|
312
|
314
|
315
|
321
|
324
|
325
|
341
|
342
|
345
|
351
|
352
|
354
|
412
|
413
|
415
|
421
|
423
|
425
|
431
|
432
|
435
|
451
|
452
|
453
|
512
|
513
|
514
|
521
|
523
|
524
|
531
|
532
|
534
|
541
|
542
|
543
|
So, at most, you have only 32 rotor sequence choices rather than 60. Of course, as the month progresses, some of the remaining 32 rotor sequences allowed by this rule would be disallowed by key design flaw #1 described above, so an attacker has even fewer rotor sequences to test.
Key Design Flaw #3
The Germans always used 10 plugboard cables. This decreased the possible key space by a factor between four and five and significantly simplified an attack by an even greater factor.
Operational Error #1
Recall that the operator was to choose two random 3-character sequences,the indicator setting and the message setting. However, humans are very bad at choosing random sequences. The indicator setting and message setting were often predictable, making a search of the key space significantly easier.
Two common pairs of 3-character "random" sequences were,
or course,
HIT,LER
and
BER,LIN,
as well as ABC and
simple keyboard sequences like ASD.
Predictable settings were referred to as "Cillies",
because one German cipher clerk with a girlfriend
named Cilia always used CIL,CIL.
Operational Error #2
The Germans used predictable cleartext sequences, providing "cribs" or probable known-plaintext attacks.
Part of this was the lexicon, the terms used in the language. Long distinctive words appeared frequently: Obergruppenführer, Untersturmbannführer, Obersturmbannführer, and other military ranks, plus common military terms including Kriegsgefangene (prisoner of war) and gefangengenommen. (captured)
Another part was the predictable structure of routine messages.
For example, weather stations that encrypted a message
every day with an identical beginning,
such as the German for:
TODAYS WEATHER IN THE
BALTIC SEA WILL BE ...
Similarly, Italian forces in North Africa utilized a
standardized surrender message sent back to Italian
headquarters immediately before surrender,
sent in Italian, of course:
WE WILL DEFEND
THE SACRED SOIL OF AFRICA
WITH OUR LAST DROP OF BLOOD X
LONG LIVE THE KING X
LONG LIVE IL DUCE X
This not only provided a crib, but a message of this length from a field unit was very likely contained the ciphertext version of this standard message. This meant two benefits for Allied forces — a crib for cryptanalysis and a clear indication that the sending unit was ready to surrender immediately and could be captured without a fight. HFDF (High-Frequency Direction Finding) was crucial to figure out just which unit was done.
Similarly, the daily garrison medical report was useful
for cribs.
Hemorrhoids are a common ailment in desert service,
but the Italians had no code word for that.
So it had to be spelled out,
LE EMORROIDI in Italian,
providing a likely crib.
[For the Italian details see
The Sigint Secrets: The Signals Intelligence War, 1990 to Today
Nigel West, 1988, ISBN 0-688-07652-1, pg 231.]
Amazon
ASIN: 0688095151
Operational Error #3
Stronger systems were deployed incrementally.
When the Navy first introduced the four-rotor Enigma, this meant an additional three rotors with unknown wiring. But the same message would be encrypted both with the four-rotor and three-rotor system, so those vessels and stations without the four-rotor system could receive the message. Since the three-rotor system was broken, this allowed the discovery of the wiring of the three new rotors in the naval 4-rotor system.
Operational Error #4
Identical messages were encrypted with multiple keys.
When submarines surfaced, they typically requested the transmission of all messages sent while they had been submerged. These old messages would be encrypted with this day's key. By matching messages based on character length, this frequently provided a match to a broadcast message that had been broken previously. This provided a complete known-plaintext attack against this day's keys.
Operational Error #5
Some messages were also sent by insecure means, providing known-plaintext attacks.
A prominent example was the provision of much information, including military cables, to the Japanese military attache in Berlin. General Hiroshi Ōshima then encrypted these messages for transmission to Tokyo using a compromised Japanese cipher. Since the Japanese system had been broken, the message could be read from the Berlin-to-Tokyo link. This provided the message itself, which might be of enormous use on its own, but it also provided a known-plaintext attack to more easily discover that day's Enigma key.
Allied General George S Marshall described Ōshima as "our main basis of information regarding Hitler's intentions in Europe."
And, as was only declassified in 1995, Ōshima's messages led to Japanese diplomatic traffic in general. That gave the Allies an insight into Japanese strategic thinking. This included the fact that the Emperor had no intention of surrender, and was not bothered by the prospect of millions of Japanese civilians dying in a suicidal defense of the home islands. This made the two atomic bombs the far less deadly choice for forcing the end of the war.
Operational Error #6
Some messages were sent in response to Allied actions, providing partial chosen-plaintext attacks.
The British referred to this as "gardening". The Allies would do something at a specific time and place, like an artillery barrage, the laying of naval mines, an obvious surveillance overflight, etc., in order to get a German unit to report it using that day's code. This revealed code words for specific locations, navigational references, and the cryptographic keys.
Allied Cryptanalysis of Japanese Codes and CiphersAlso see how the U.S. enticed the Japanese into reporting on a non-existent problem with water desalination systems on Midway Island, in order to determine the Japanese code word for that island.
Hubris
The Allies were careful to not make too much use of the ULTRA data, so as not to encourage the Germans to suspect their system had been broken. But even when the U-boat operations in the Atlantic were largely shut down, Dönitz refused to believe that it was because of cryptanalysis — he continued to believe that any communications insecurity was due to espionage.
The Allies interrogated a number of German cryptologists after the war. Several of them said that they knew that the Enigma system had vulnerabilities and had reported this up the chain of command. However, it was thought that the Allies would not expend the effort needed to break the system.
Japan's Imperial Fleet used codes rather than ciphers, such as the several JN25 code variants. Their Foreign Ministry used cipher machines, called PURPLE by the Allies. Japan made similar mistakes, including perhaps most significantly the belief that their system was unbreakable.
Amazon
ASIN: B00RY85CQI
Amazon
ASIN: 069116472X
The Imitation Game
The 2014 film The Imitation Game was loosely based on the book Alan Turing: The Enigma by Andrew Hodges. I think that as movies go, it did a reasonable job of showing the history. It correctly showed some of the technical details, like the use of partial known-plaintext "cribs" and the "menu" diagrams. Also some relatively minor details, like showing intercept operators writing down the actual Morse code groups we hear on the soundtrack. My biggest complaints about historical inaccuracies are:
- Portraying Alan Turing with severe psychological and social problems, surrounded by conservative, almost stuffy, co-workers who barely tolerate him. Turing wasn't nearly the most eccentric person at Bletchley Park.
- Conversely, portraying Alastair Denniston as the Frank Burns of British military intelligence. Bletchley Park had a fairly academic atmosphere with several rather eccentric people in crucial roles.
- Showing four young workers making major decisions about naval missions. Interception, decryption, translation, and analysis were separate stages, at which point the intelligence was sent to high-ranking military officers and political leaders for decision-making.
Other than that, I thought it was good, more accurate than many supposedly historical movies. Others have compiled significantly longer and more detailed lists of complaints about historical accuracy.