Reverse-Engineering the Hacker
What types of passwords will a typical hacker guess?

Advice Dog, from the handy Meme Generator.
I configured a collection of eight Linux machines at a major university in the midwestern U.S. to send their syslog output to another Linux machine on my desktop. I had installed denyhosts on that system on my desk, so it quickly comes to ignore repeated SSH password guessing failures. But the other systems are default (or very nearly so) installations of Ubuntu and so they let the remote hackers keep guessing and guessing.
Normally this voluminous log data is just input for my statistical or textual analysis, as described on another series of pages where I show how to apply textual analysis tools built from simple Unix commands to recognize common attack patterns.
Recently, however, a clumsy hacker provided some useful information and an interesting insight into the details of a typical attack!
The host at IP address 109.239.138.2 launched a fairly aggressive SSH password guessing attack. Denyhosts on my desktop machine blocked it after 11 failed guesses. But it made 2,382 failed password guesses on seven of the other eight logging Linux hosts, and just 1,087 on the eighth (I think this was because that machine coincidentally happened to be shut down for part of the day).
IP address 109.239.138.2 does not resolve to a
fully qualified domain name, but we can easily see with
whois
that it is assigned to a
Russian
ISP.
Trimming some of the output:
% whois 109.239.138.2
[....]
% Information related to '109.239.128.0 - 109.239.143.255'
inetnum: 109.239.128.0 - 109.239.143.255
netname: RU-ETELECOM-20100204
descr: JSC GLOBALNET
country: RU
org: ORG-ET23-RIPE
admin-c: VVV27-RIPE
tech-c: VVV27-RIPE
status: ALLOCATED PA
mnt-by: RIPE-NCC-HM-MNT
mnt-lower: ETELECOM-MNT
mnt-routes: ETELECOM-MNT
source: RIPE # Filtered
organisation: ORG-ET23-RIPE
org-name: JSC GLOBALNET
org-type: LIR
address: GlobalNet JSC
Vladimir Vedeneev
Kolomyagskiy 18
197348 St.Petersburg
RUSSIAN FEDERATION
phone: +78129301210
fax-no: +78123493530
e-mail: vvv@gblnet.ru
mnt-ref: RIPE-NCC-HM-MNT
mnt-ref: ETELECOM-MNT
mnt-by: RIPE-NCC-HM-MNT
source: RIPE # Filtered
person: Vladimir V. Vedeneev
address: P.O. Box 146, Road Town, Tortola, British Virgin Islands
e-mail: vvv@gblnet.net
phone: +357 25 155 293
nic-hdl: VVV27-RIPE
mnt-by: MNT-GLOBAL-NET
source: RIPE # Filtered
[....]
% Information related to '109.239.138.0/24AS31500'
route: 109.239.138.0/24
descr: Bergoltz P2P Customer Network
origin: AS31500
mnt-by: MNT-GLOBAL-NET
source: RIPE # Filtered
British Virgin Islands?
Whatever....
Meanwhile,
traceroute
suggests that the host is in
Sankt-Peterburg,
as it is within
four hops and a few milliseconds away from
bm18-1-gw.spb.runnet.ru:
% traceroute -f 12 109.239.138.2 Skipping 11 intermediate hops 12 te8-2.ccr01.ams03.atlas.cogentco.com (154.54.0.69) 143.91 ms 142.902 ms 138.943 ms 13 te2-1.mpd01.ams04.atlas.cogentco.com (130.117.49.10) 136.246 ms 138.341 ms 136.160 ms 14 runnet.demarc.cogentco.com (130.117.23.62) 142.377 ms 137.222 ms 141.31 ms 15 tele-1-gw.sth.runnet.ru (194.85.40.242) 171.744 ms 171.777 ms 172.556 ms 16 tug-1-gw.sth.runnet.ru (194.85.40.173) 173.166 ms 174.89 ms 178.854 ms 17 bm18-1-gw.spb.runnet.ru (194.85.40.141) 173.262 ms 170.620 ms 172.798 ms 18 c7606-te4-5-291.gblnet.ru (194.190.254.182) 184.944 ms 171.533 ms 185.5 ms 19 bm18-bm18v2-te-gw.gblnet.ru (94.124.181.185) 171.517 ms 173.430 ms 171.569 ms 20 b57-bm18-te-gw2.gblnet.ru (94.124.181.250) 171.284 ms 172.310 ms 174.46 ms 21 109.239.138.2 (109.239.138.2) 175.165 ms 173.535 ms 183.548 ms
Further investigation could look at the IP block assignment or routing information if we cared to dig deeper.
The attacking host was guessing passwords on all of the target systems at once (all these are on a /24 subnet), so the sequences of SSH authentication failures were overlaid in the same block of time in the syslog output. A failed SSH authentication for an existing account appears like the following. In this output:
- The SSH daemon on the target host has PID 1998.
- The remote (attacking) host is using its client TCP port 34438.
- The connection was made using the SSH2 protocol (as it should, the hosts are configured to drop connection attempts via SSH1).
-
The target SSH server's hostname has been replaced
with
hostname.
Feb 25 20:00:11 hostname sshd[1998]: Failed password for root from 109.239.138.2 port 34438 ssh2
On the other hand, a failed SSH authentication for an account that does not exist on the server appears like this:
Feb 25 20:31:47 hostname sshd[1998]: Failed password for invalid user oracle from 109.239.138.2 port 34237 ssh2
So, let's see how the attack was distributed across the targets. The hostnames have obviously been changed in this output:
% grep 'Failed password.*109.239.138.2' /var/log/authlog-common > guesses
% awk '{print $4}' guesses-109.239.138.2 | sort | uniq -c
2382 target1
2382 target2
1087 target3
2382 target4
2382 target5
2382 target6
2382 target7
2382 target8
11 bobsdesktop
This went fairly quickly. The attack started at 20:00:11 local time and ended at 22:49:05, so an average of one guess every 4.26 seconds on each host and 1.75 guesses per second coming into the subnet. One guess every 4.26 seconds means going about as quickly as a single-threaded SSH password guessing attack can possibly go against one of these servers. These attacks are not meant to be subtle — there is little need for subtlety since most people ignore their logged SSH failure events.
This table includes more detail. The hosts have been ordered by IP address. Notice what that does to the start times. I believe that the attack was against the entire xx.yy.zz.0/24 subnet. There was one process or thread per target IP address, all of these running simultaneously and independently. They were started quickly in order of IP address, and completed in very similar times but without having kept in sychronization.
| Server | IP | Start time | End time | Guesses |
bobsdesktop |
xx.yy.zz.53 |
20:00:11 |
20:00:45 |
11 |
target8 |
xx.yy.zz.121 |
20:02:32 |
22:47:54 |
2382 |
target7 |
xx.yy.zz.200 |
20:05:08 |
22:48:49 |
2382 |
target1 |
xx.yy.zz.201 |
20:05:08 |
22:49:05 |
2382 |
target2 |
xx.yy.zz.202 |
20:05:11 |
22:48:19 |
2382 |
target3 |
xx.yy.zz.203 |
20:05:12 |
21:19:53 |
1087 |
target4 |
xx.yy.zz.204 |
20:05:12 |
22:49:04 |
2382 |
target5 |
xx.yy.zz.205 |
20:05:17 |
22:49:42 |
2382 |
target6 |
xx.yy.zz.206 |
20:05:19 |
22:48:48 |
2382 |
Which existing accounts did the hacker try to break? The system administrator was the primary target:
% grep -v 'invalid user' guesses | awk '{print $9}' | sort | uniq -c
6 ftp
16 mail
16 mysql
14 nobody
16 proxy
6627 root
14 sync
16 www-data
OK, that's nothing new.
Notice how common the counts of 14 and 16 are.
That means two password guesses for each account on each
of the 7 or 8 target hosts.
The log shows that they tried all the root password
guesses first, then it goes to a list of others.
The set of invalid accounts for which it tried to guess
passwords is far more interesting.
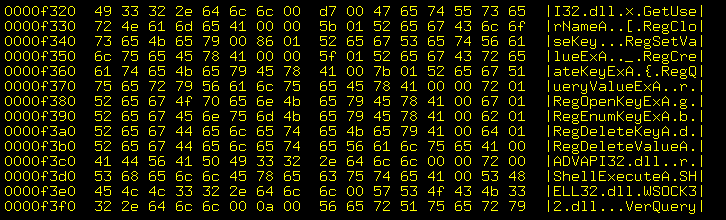
This was another case of a hacker transposing columns in the
data file used after the long list of root password guesses.
What was intended as "login password" was treated as
"password login", and so the list of invalid users is
really the list of passwords the hacker thought might
be in use.
Most appear 14 or 16 times (intended as guesses for two
accounts per target, probably root and one other),
some appear 28 or 32 times (so four accounts per target),
one of them 656 times (which is 41*16).
One lesson here is that while
!QAZ@WSX#EDC
or
0m9n8b7v6c5x4z
may look like awfully complicated passwords,
they really aren't.
Look at your keyboard, they are really very simple to remember
and type!
The hackers know that keyboard sequences are popular because
they're easy to remember and type but they satisfy fairly
dumb password quality rules.
Other popular guesses, therefore inappropriate password
choices include your name:
abdul, adrian, adriene, ...
software you use or its default password:
asterix, apache, apache1q2w3e4r, cvsadmin, dump, oracle,
...
pop culture icons:
asterix (again), bradpitt, finalfantasy,
...
and the classics:
admin, changeme, passpass, passwd123, ...
The following shows what were intended to have been the password guesses and the number of times each was meant to have been used against a group of seven or eight targets:
% awk '/invalid user/ {print $11}' guesses | sort | uniq -c
14 !QAZ@WSX#EDC
14 0123
14 01230123
14 0147
14 0147258369
28 0m0n0b0v
14 0m0n0b0v0c0x0z
14 0m9n8b7v6c5x4z
14 0okm9ijn
14 0okmnji9
14 0okmnji98uhb
14 0qa9z87w6s5x4e3d2c1
14 0z0x0c0v
14 0z9x8c7v
14 12345qwert
14 1234qwer
14 123fedora
14 123manager
14 123mysql
14 123q123a123z
14 123q123w123e123r123t123y
14 123qwe
14 123qwe123qwe
14 123server
14 123system
14 123www
14 12z12x12c
14 147
14 147258
14 147258369
14 147852
14 159357
14 1a2a1s2s1d2d
14 1l1k1j1h1g
14 1l2k3j4h
14 1m2k3o
14 1m2k3o4n5j6i
14 1p1o1i1u
14 1p2l3,4m5k6o
14 1p2l3m
14 1p2l3o4k
14 1p2l3o4k5i6j
14 1p2o3i4u
14 1p2o3i4u5y
14 1p2p3o4i
14 1q1a1z1x1s1w
14 1q1a1z2w2s2x
14 1q1a1z2w2s2x3e3d3c
14 1q1a1zx2s2w2
14 1q1q1q1q1q
14 1q1q2w2w3e3e
14 1q1w1e1r1t1y
14 1q2a3z
14 1q2a3z4w5s6x
14 1q2q1w2w
14 1q2w3e
14 1q2w3e1q2w3e
14 1q2w3e4r
14 1qa11z
14 1qaz2qaz3qaz4qaz5qaz
14 1qaz2wsx
14 1qaz2wsx3edc4rfv5tgb
14 1qaz3edc
14 1root2root
14 1z1x1c1v1b
14 1z2a3q
14 22
14 2222
14 22ssh
14 258741
14 258963
14 2q2w2e2r2t2y
14 3210
14 321654987
14 321ewq321ewq
14 3333
14 369852
14 3q3w3e3r3t3y
14 3wa2q1
14 4444
14 4rfvbgt5
14 5555
14 5a4s3d2f1g
14 5a5s5d5f
14 5rdx6tc
14 5rdxcft6
14 5rdxzse46tfc
14 5tgb6yhn
14 5tgbnhy6
14 5z4a3qx2s1w
14 6666
14 6tgv
14 741
14 741852
14 741852963
14 753159
14 7777
14 789456123
14 7ygv
14 7ygv6tfc
14 7ygvcft6
14 852147
14 8888
14 8uhb
14 8uhb7ygv
14 8uhbvgy76tfc
14 951753
14 963852741
14 9999
14 9ijn
14 ACCOUNTS
14 APACHE
14 DNS
14 HTTPD
14 LINUX
14 NOTES
14 ORACLE
14 PASSWD
14 PASSWORD
14 Password
14 R00t
14 REDHAT
14 ROOT0123
14 ROT
14 ReelBox
14 Root
14 USER
14 USERTEST
14 Valhalla
14 WEBADMIN
14 WEBMASTER
14 a123
14 a1s1d1f1g1
14 a1s1d1f1g1h1j1k1l1
28 a1s2d3
14 a1s2d3f4
14 a1s2d3f4g5
14 abdul
14 abi
14 abinnovative
14 abuse
14 access
14 accounts
14 accounts123
80 admin
14 adminlinux
16 adriaan
16 adrian
16 adriene
16 adrion
16 aegis
14 ahmed
14 alexander
16 alexandre
16 alfonso
16 alizarraga
16 alpha
14 america
14 amjamani
14 amy
16 andre
16 andreas
14 andrei
16 andrey
16 andreyy
64 anunez
14 aol
14 apache
14 apache123
14 apache1234
14 apache1q2w3e4r
16 apollo
16 araceli
32 archivo
16 aron
14 arul
14 arun
14 ashpri
14 assettracker
16 asterix
16 atul
14 babu
14 bak
14 balaji
14 barney
14 bash
14 bashhistory
14 best
14 bhu8vgy7
14 bianca
14 bluescope
16 bogon
16 borg
14 bradpitt
14 brewbuilder
32 bureau
14 camera
14 car
14 career
28 carol
14 cat
14 cde3xsw2zaq1
14 cdexswzaq123
14 cdrw
14 chalse
16 changeme
28 china
16 cliente
14 clients
16 clopez
56 code
14 coder
14 colin
16 compras
96 copia
14 cvs
14 cvs123
14 cvsadmin
14 cvsuser
14 cvsuser123
14 damian
16 danger
16 dangerous
14 dani
16 daniel
16 david
16 db2fenc1
14 debian
14 default
30 demo
16 desarrollo
14 digitallibrary
14 dns
14 dns123
14 dnsdns
14 dnswww
14 dump
14 e3e3w2w2q1q1
16 edgar
16 edilson
14 edu
14 eduard
14 efront
16 eggdrop
16 elastix
14 elena
16 eric
14 erp
16 export
14 external
16 fabio
14 fax
14 fax123
14 fedora123
14 finalfantasy
16 financiero
14 firewall
14 force
14 fotbal
14 francois
14 freebsd
14 friday
24 ftp
14 ftp123
14 ftpd
14 ftptest
28 ftpuser
14 ftpuser123
14 fuckyou
16 garcia
16 gast
16 gaston
14 gcarter
16 gerencia
15 gestionale
16 global
14 gnanam
16 gonzales
16 gorrion
16 gregorio
14 gsm
80 guest
14 han
14 harvard
16 henri
32 henry
14 history
48 home
16 host
16 hosting
16 hostmaster
16 hosts
14 httpd
14 httpd112233
14 httpd123
14 httpd1234
14 httpds
14 ice4budu
14 images
14 ina
44 info
14 infoinfo
14 internet
16 intranet
14 ivan
14 jaime
14 jana
14 jean
14 jenny
14 jeyarman
14 jhon
14 jhon123
16 jmurphy
16 john
14 johnite2
14 johnson
16 johny
14 junior
16 kerp
14 kevin
14 kiruba
14 knoppix
14 kpi
14 kts
14 la
16 laboratorio
14 lakshmi
14 laura
14 levis
14 library
32 linux
14 linuxadmin
14 linuxredhat
14 linuxshell
16 lisa
14 lnlifecare
14 lost+found
16 lx
14 m0n9b8v7
14 maehswari
30 maggie
16 magie
44 manager
28 manager123
16 maraujo
14 marco
14 marco123
14 mari
14 mark
16 martin
80 master
14 matt
14 matt123
14 michael
16 mihai
14 mko
14 mkonji
14 mkonjibhu
14 mnbvcxz
14 mohan
16 morris
16 mtapia
14 muthu
48 mysql
16 mysql1
14 mysql123
14 napolian
16 nathan
14 neil
14 netbeans
16 netmon
16 network
16 nologin
14 notes
14 notes123
14 notes1234
14 notes1q2w3e
16 office
14 okm
14 okmijn
14 okmijnuhb
14 online
14 onlineexam
14 onlinetest
14 optisol
656 oracle
16 oracle1
14 oracle1q2w3e
14 oracleroot
14 order
14 oscar
14 p0o9p0o9
14 pack
14 panner
16 paradise
14 pass
14 passpass
14 passwd123
14 pasumpon
48 patricia
16 pcs
16 pgsql
16 pharmos
16 polarisnet
30 postgres
14 postgres123
16 primaveras
14 print
14 project
14 project_abi
48 proman
16 pronto
16 prostejov
14 prya
14 public
14 public!@#
14 public123
14 public1234
14 q11qw22w
14 q11qw22we33e
14 q1w2e3
14 q1w2e3r4t5
14 q1w2e3r4t5y6
14 qawsedr
14 qazwsxedcrfv
14 qwer123
28 qwer1234
14 qwer123456
14 qwerqwer
14 qwert12345
14 qwertyu
14 qwertyui
14 qwertyuio
14 qwertyuiop
14 r00t
28 radmin
14 raj
14 raja
28 rajesh
14 rakesh
14 ralph
14 ram
14 ray
16 redhat
14 redhat13579
14 redhat1q2w3e
14 redmine
14 rfpg
16 rgarcia
14 rootedu
14 rootoracle
14 rootuser
14 rootuseradmin
16 rosemari
16 rosemary
32 rosestreetlabs
14 rot
14 sabari
14 sabarish
14 sadhana
42 sales
28 sales123
14 sales1234
16 santiago
16 santodomingo
14 sara
14 sarah
14 saurav
14 scott
14 sebastian
16 secret
14 selva
206 server
14 server123
14 serverpri
28 service
14 service1234
16 severino
16 shenlong
14 shing
14 shop
16 shoutcast
14 simens
16 simon
14 soccer
16 sparada
14 ssh22
14 staff
14 stage
14 stephanie
14 steve
16 student
14 students
14 suganya
14 sun
14 sun0s
14 sun123
14 sunos
14 sunos123
16 suporte
192 support
14 suresh
14 svn_abi
16 sysadmin
28 system
28 system123
16 tagus
16 teamspeam
14 tech
14 tech123
48 telnet
128 test
16 test1
14 test2
14 test4321
62 teste
14 teste123
32 tester
14 testftp
14 testing
84 testtest
16 tomas
30 tomcat
14 tomcat123
16 tribox
16 tryxbox
14 turbo
16 ubuntu
14 united
14 univers
14 university123
14 university123123
48 upload
32 user
16 user1
14 userftp
48 username
14 userroot
14 usertest
14 usr
128 usuario
16 usuario1
16 vendas
14 vgy76tfc
14 vgy7cft6
16 vicente
14 vijay
14 vincent
28 virtual
14 virtual1
16 vugar
14 wallace
74 web
14 web123
14 web1234
30 webadmin
44 webmaster
14 webweb
14 webweb123
14 webwebweb
16 weed
16 wellington
14 will
14 wilson
14 windows
28 work
14 www
14 www111
14 wwwwebmaster
14 wwwwww
32 xbox
16 xforte
14 xsw21qaz
14 xsw2zaq1
14 z0x9c8v7
14 z0x9c8v7b6
14 z1x1c1v1b1
14 z1x1c1v1b1n1
14 z1x1c1v1b1n1m1
14 z1x2c3
14 z1x2c3v4b5
14 zaq12cde34
14 zaq12wsxcde34
14 zaq12wsxcde34rfv
14 zaq12xsw34cde
32 zenoss
14 zxcvb