Cryptographic Terminology
Basic Terms
We need to start by defining some fundamental terminology used to discuss cryptography and introducing the basics of encryption and decryption.
Plaintext or Cleartext
This is the original message. It could be simple text, or a JPEG image, or a zipped archive file, or whatever you want to protect. Sometimes this is called "cleartext".
Ciphertext
This appears to be highly random, as the actual information contained in the plaintext has been hidden. The term in math or information theory is that the ciphertext has high entropy.
Cipher
This is the algorithm that converts plaintext to ciphertext, and vice-versa.
Key
A key modifies how the cipher works on one run. We know that our adversary knows which cipher we're using, and they have a copy of it. Security is based entirely on protecting the keys. Keys are binary strings, or if you want to think of them another way, the large numbers that those binary strings could represent.
Computationally difficult
Possible in theory, but a practical attacker will not have the time (or the motivation, or other needed resources) to carry out an exhaustive attack, nor will they be so lucky as to stumble upon the answer unexpectedly early. It's "hard enough" that it's not realistic to worry about an adversary solving this problem so quickly that they can use the result against us.
Codes and Ciphers
A code is a scheme for replacing words,
names, and phrases.
The result looks like the original language but the
meaning is obscured.
For example, the Imperial Japanese Navy used
EAST WIND, RAIN
(in Japanese, of course)
as a coded message to launch the attack on Pearl Harbor.
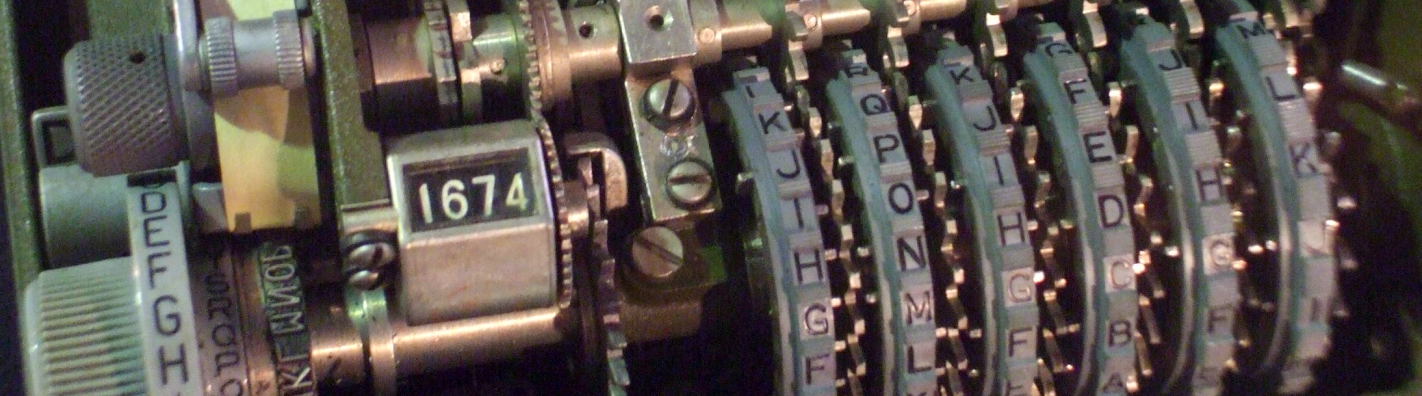
A cipher operates at the level of individual
bits.
Historical ciphers operated on individual letters or
small letter groups.
It should be meaningless random data,
revealing only that a message of a certain size
was transmitted at a certain time.
An enciphered version of
ATTACK PEARL HARBOR 7 DECEMBER
might look like:
NAMKE PIRCI YEAXW GUOCY HIJXU AARUD
Admiral Isoroku Yamamoto, master strategist of the Imperial Japanese Navy.
Codes and ciphers are typically used in combination. The message is first modified by replacing specific terms, names, and locations by code words. The result is then enciphered.
For example, during World War II the Allies had broken the JN-25 cipher used by the Imperial Japanese navy. They could read the cleartext, but code words were used. The US knew that the Japanese fleet was going to attack a location referred to as "AF" in June 1942, but they did not know whether "AF" was code for Midway Island or a location in the Aleutian Islands.
Midway was instructed to transmit cleartext messages falsely reporting that their water desalination plant was broken. The Japanese fleet intercepted these and then sent messages that decrypted to the Japanese for "AF is short of water". That revealed the meaning of the code group "AF" and allowed the US to win the crucial Battle of Midway.