
Misadventures in Teaching —
Let's All Hide Our Heads in the Sand
My plan seemed reasonable for a networking course
I would use a web browser to connect to a web site that no one had used all week long, guaranteeing fresh network traffic. The point was to observe some details of network protocols. The content of the web page didn't matter, it just needed to be something that no one had viewed all week so were were retrieving fresh data, nothing from a local cache. I needed to demonstrate a few networking concepts:
DNS and how we're usually trusting cached non-authoritative DNS records.
HTTP and how both the client (the browser) and the server very openly volunteer information about their version and at least some information about of the underlying operating system.

To provoke a fresh DNS lookup, and get their attention (as I was teaching in the Washington DC area), I used www.fsb.ru, the web site of the Федеральная Служба Безопасности or Federalnaya Sluzhba Bezopasnosti, the Federal Security Service. This is what used to be the KGB or Комитет Государственной Безопасности, the Komitet Gosudarstvennoy Bezopasnosti or the Committee for State Security.
I first put my system's display up on the video projector. Then I started the excellent Wireshark protocol analyzer, and had it filter the captured packets to save only those packets sent to and from my system.
Then I started the Firefox browser. I brought up the FSB web page, pointed out the URL, and very briefly told them what we were looking at.
Then I right-clicked one of the HTTP packets in the Wireshark trace and selected "Follow TCP Stream". I would come back and look at the DNS packets later. The extracted TCP stream started like the following, with outbound from my client in red and inbound from the server in blue. The FSB's web site runs on Apache on some form of Unix, that's no surprise:
GET / HTTP/1.1 Host: www.fsb.ru User-Agent: Mozilla/5.0 (X11; OpenBSD amd64; rv:18.0) Gecko/20100101 Firefox/18.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Connection: keep-aliveHTTP/1.1 200 OK Date: RContent-Type: text/html; charset=utf-8 Content-Length: 10026 Last-Modified: RConnection: keep-alive Keep-Alive: timeout=5 Server: Apache/1.3.39 (Unix) Accept-Ranges: bytes <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"> <html> <head> <title>.......
Ow! Our retinas!
Meanwhile, a student in the front row was still squinting at the all Russian content in the web browser, leaning her head to the side as if that really could help her to see around the Wireshark window hiding most of the FSB home page. She stopped me, asking "Wait, what's on that web page? I can't read it!"
Well, it is written in Russian, I don't suppose you happen to read Russian, do you?
"Russian?! Oh no, I can't read that!"
That's fine, I can tell you generally what we're seeing there, but the page content isn't the point. I just loaded that page so we could look at the packet trace. I added that reading Russian web content would not be on the quiz at the end of the week. But as usual in these scenarios, my subtle wit was completely wasted.
"But why is that page in Russian?!"
Well, that only makes sense, it is a Russian government agency, after all.
"Russian government!? What is that web site!?"
Oh, I thought I had mentioned that. [Actually I'm quite certain that I did that just a moment ago.] It's the FSB, which is the new name for what used to be called the KGB.
"The KGB!? We shouldn't be looking at that!!!"
It's OK, you aren't at work, we're in a classroom at a training center. I just used this to get fresh DNS information, obviously none of you had looked at this site this week, and ...
"No, no, I mean that it's a secret organization! We shouldn't be looking at that!!"
Uh, I guess you'll have to trust me on this if you can't read Russian, but right here on the page, where it says пресс-слуба or press-sluzhba, that means "Press Office". They want people to read the content on their site. Here, let's look at that press office page. See, various announcements to the media about what the FSB has been up to lately, and ...
"No, no, this is a secret organization! No one outside that organization knows about it, and so no one knows that this web site exists. No one ever looks at this web site."
Uh... I don't work for the FSB, I swear, and I know that they exist. They're mentioned in newspaper and magazine articles all the time, and if you don't know their URL you can just ask Google.
"No, that isn't right."
Then she bowed her head and looked down at the table until I was done. She was going to keep her head buried deep in the sand even if the rest of us in the room insisted on our bizarre misbehavior. She seemed to think that everyone studiously ignores everything they are not told to look at.
Wikipediapage about
NRO NRO
press
office NRO
web
site
She worked for the National Reconnaissance Office, the U.S. intelligence agency that designs, builds and operates the U.S. government's spy satellites. Well, it's not as if the NRO has its own web site.
Actually, they do. But it's not as if the NRO has a press office.
Actually, they do. But at least it's not as if there's a Wikipedia page about the NRO.
Actually, there is, it's part of a collection of 24 pages in the category "National Reconnaissance Office", accompanied by subcategories of 23 pages about specific NRO satellites and 16 pages on present and past directors of NRO.
I didn't mention any of that to her, we seem to have already come awfully close to making her head explode.
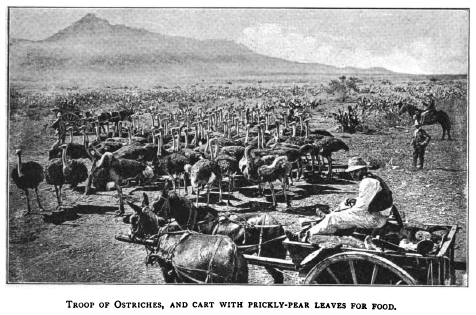
Troop of ostriches, and cart with prickly-pear leaves for food. From Home Life on an Ostrich Farm by Annie Martin, 1890.