
VLAN — Virtual LAN Technology
Building Switched Ethernet Networks
VLAN or Virtual LAN technology has several advantages. It can make a network cheaper and simpler to build, and easier to maintain and modify. Let's see how to apply VLAN technology.
Let's think first about your ideal and simplified networking environment.
All your devices — your servers, clients, printers, and the routers connecting you to other networks and out to the rest of the Internet — would be interconnected with Ethernet switches. The devices and their switch ports would run in full-duplex mode at an adequately high speed.
The fact that it's a switch rather than a hub (also called a concentrator or a repeater back in the era when hubs were still used) means that your actual data throughput might be 80% of the actual wire speed, as opposed to 10% and down.
The switch also provides some defense against packet sniffing
and the collection of passwords and other sensitive data by
unauthorized hosts.
Just some protection, not really all that much, as there are
attacks that can confuse the ARP caches of the end points
and trick them into rerouting data inappropriately with
little to no sign.
Go get arpspoof,
part of the
dsniff package,
if you want to investigate this.
You would want to partition your traffic into relatively
small subnets for two reasons.
First, security: a sniffing attack based on
arpspoof
only works when the attacker is on the same LAN.
Smaller number of hosts per LAN means either smaller chance
that you are on the same LAN as the attacker, or a smaller
number of targets available to a hacker, however you want
to look at it.
Second, better data throughput.
So, you would go out and buy a number of switches, at least one per subnet. Subnets spanning multiple switches would require those switches to be cabled together. Then run an Ethernet cable from each node to the appropriate switch. Next, connect the multiple ports of one or more routers into the switches, one per switch, to connect the subnets. Finally, configure the routers and individual hosts.
There are two problems with this approach.
First, your subnets are probably going to be of widely varying sizes. A backbone connecting the subnets together needs only as many ports as there are subnets, presumably plus one to connect to the router leading toward the Internet. Meanwhile some other subnets might have dozens of hosts. You will have to buy (and support) a wide variety of hardware, and you will end up with "wasted ports", switches with maybe 48 ports but 10-20 of them going unused.
Second, when you decide that a number of hosts need to be relocated from their original subnets to other subnets, at the very least you have some cables to be re-run. More likely, you need to buy more hardware because one of the switches just ran out of ports.
What you're doing looks like the following. Let's say you have two subnets, A and B, and two rooms with network hosts, rooms 1 and 2. You will need to connect things like this, where the letters "A" and "B" label individual hosts on those subnets.
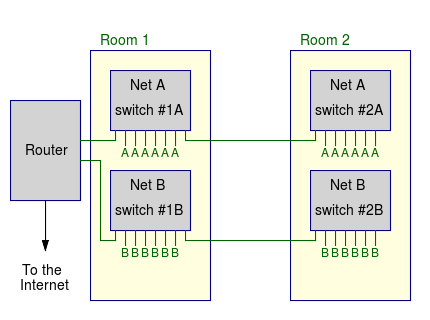
Yes, used switches are pretty cheap on eBay, but this involves a stack of switches in every room. We may have to add another switch if we move just one host from its original subnet to another. Worse yet, what if we decide to add another subnet to further partition the traffic?
VLAN technology solves these problems!
You need to program your collection of switches to partition themselves into multiple virtual LANs. The switch only forwards frames between ports on the same VLAN. Put another way, each VLAN is its own broadcast domain. It also has a unique logical IP address block. You can reconfigure which VLAN a physical port belongs to, and effectively move a host to a new LAN without changing any cabling.
The packets have to pass through a router to travel between VLANs. The VLANs logically partition the large physical LAN to increase security. Routers can forward packets between VLANs, subject to any packet filtering rules. This could lead to the odd looking situation of a router with multiple Ethernet interfaces plugged into the same switch.
What you really do is set up multiple subinterfaces on the one physical interface. Just one cable from the router to the switch, but at a logical IP layer it's as if it were two connections. You program that switch so the port where you plug in the router belongs to multiple VLANs.
Multiple switches can be connected via a trunk connected to specially designated ports. You probably will use the IEEE 802.1q trunking protocol to forward traffic between switches. It inserts a 32-bit field between the source MAC address and the Ethertype fields. Cisco switches can run the proprietary DTP Dynamic Trunking Protocol.
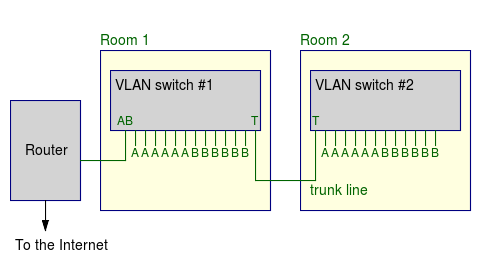
In the above example, every host on VLAN A is directly connected to every other VLAN A host and can send a frame directly across the trunked switches. But to send a packet to host on VLAN B, it would see that the destination's IP address was on another logical network, and so it would send it to the router port on VLAN A. The router would then transmit it out its VLAN B port.
IP RoutingLogic
The packet would have to be forwarded through the router, because the switches refuse to forward frames between VLANs. The router would then send the packet directly across the other VLAN from its port connected to the appropriate VLAN.
If you want to experiment with this, VLAN-capable Cisco 2900-XL 100 Mbps switches are available used on eBay for $30-60 each including shipping.

Rack of Ethernet switches.