Computer System and Network Security
Cybersecurity
Cybersecurity becomes more important every year,
as we rely more and more on the world-wide
Internet in government, business, and our
private lives.
Everyone needs to know how to be safe enough in their
personal email and web browsing.
Start with my
introductory page
if you're new to cybersecurity.
Certifications are the coin of the realm nowadays,
and they're the main reason many people come to this page.
And so, here's my guidance on preparing and passing the exams:
The rest of these pages provide background for the courses
I write and teach.
They list the references and URLs for various tools,
studies, news reports, and other things that come up
in courses.
I use these pages myself, so I don't have to try to
memorize URLs and other reference details!
Here's that starting point:
Cybersecurity Basics
How to stay safe online
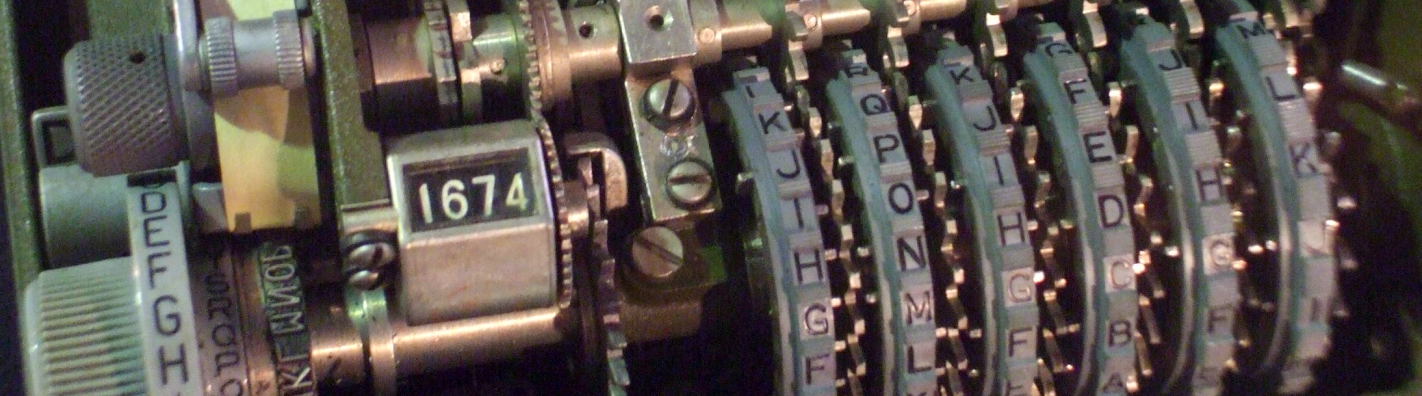
Few persons can be made to believe that
it is not quite an easy thing to invent a
method of secret writing which shall baffle
investigation.
Yet it may be roundly asserted that human
ingenuity cannot concoct a cipher which
human ingenuity cannot resolve.
— Edgar Allan Poe, in "A Few Words On
Secret Writing", Graham's Magazine,
July 1841
Internet threat warnings
I find these to be helpful sources of information on current events and trends:
Krebs On Security SecureList US-CERT Current Activity Flashpoint Intelligence Corner

Internet security "global dashboards"
Some of these are useful, some have a relatively high level of hype, but you might find some of these useful:
Oracle Internet Intelligence
Kaspersky
DShield
Internet Traffic Report
SANS Internet Storm Center
Live Digital Attack Map
Security Wizardry Computer Network
Defence Situational Awareness
Where to go from here
Make sure you understand your systems well, and set them up properly! As Hippocrates said, "Primum non nocere", or "First, do no harm."
Be aware that your browser always gives away some information about you, unless you are using Tor and using it very carefully. Your browser just provided this information:
| REMOTE ADDR | 18.226.251.68 |
| REMOTE PORT | 35702 |
| HTTP REFERER | https://cromwell-intl.com/security/crypto/ |
| HTTP USER AGENT | Mozilla/5.0 AppleWebKit/537.36 (KHTML, like Gecko; compatible; ClaudeBot/1.0; +claudebot@anthropic.com) |
| HTTP ACCEPT | */* |
| HTTP HOST | cromwell-intl.com |